Behind the Internet Wheels of Steel - Recording Live From Somewhere - Mixing the Fresh Beats of Technology, Intelligence, Science & Security together with the occasional bass-heavy break of Humor.
"There is no security on this earth, there is only opportunity"
- General Douglas MacArthur (1880-1964)
Friday, September 29, 2006
NIST: Guidance for Securing RFID Systems
The document is titled "Guidance for Securing Radio Frequency Identification (RFID) Systems".
Does it cover all the major points of concern? You tell me. I just saw it and haven't had a chance to read it.
Thursday, September 28, 2006
Microsoft - Holy Rusted Metal Batman
Another Office 0-day vulnerability has surfaced from the underground digital ocean, this time in Powerpoint.
Also, MSF has been updated to include the SetSlice() exploit. This vulnerability was released in HD Moore's MoBB on July 18th. Lets hope that a public exploit is enough to make Microsoft take this issue serious....and make the time to get it patched.
Perhaps a little less time attempting to fix the broken DRM is in order......but I doubt it will happen. Here is the equation for producing patches, it seems.
DRM = Money for MS
Active Public IE Exploit = Money for "Real Bad Guys"
Which would you fix first?
Wednesday, September 27, 2006
Removing Natural Gas From the Ethanol Production Equation
Burning natural gas to produce all that heat is the second largest expense at most ethanol plants -- trailing only the cost of the corn used for ethanol production. One estimate says Iowa's annual production of more than one billion gallons of ethanol accounts for about 16 percent of the state's demand for natural gas.
That has Iowa State University researchers working with an Ames company to develop a renewable and cost effective alternative to the natural gas burned by most ethanol plants.
The technology involves partial combustion of biomass -- that could include corn stalks, distillers grains, waste wood or other biorenewables -- to produce a mixture of hydrogen, carbon monoxide, methane and other flammable gases. The resulting mixture is known as producer gas and it can replace natural gas in an ethanol plant's heaters. The producer gas can also be upgraded to what's known as syngas, a mixture that can be converted into high-value transportation fuels, alcohols, hydrogen, ammonia and other chemicals.
Producer gas is made by injecting biomass into a fluidized bed gasifier, a thermal system that pumps air up through a bed of hot sand, creating bubbles and a sand-air pseudo fluid. A reaction between the biomass and the hot sand-air mixture produces flammable gases. The process also generates its own heat to sustain the reaction. It's a system that's reliable, produces few emissions and can be efficiently integrated into a plant's existing natural gas boilers and dryers.
Tuesday, September 26, 2006
Microsoft Releases VML Patch
I am glad they didn't wait until the next Patch Tuesday to release this patch. It is my view, a patch should never been held for Patch Tuesday.
As a former SMS admin, I know why Patch Tuesday is important for the corporate types...but I also know that corporate PCs make up a very small percentage of zombies and spam bots on the internet. Home users are normally unaware of current exploits, patch trends and rarely have anti-spyware tools or anti-virus software.
Which group of computers do you believe are more dangerous to internet users as a whole? Corporate PCs or home PCs?
Home PCs, of course. Then why is Microsoft holding patches back just to make paid security professionals not work on weekend? All the while leaving the home users out to dry.
Release patches when they pass testing....and forget about the second Tuesday of the month. "Limited attacks" or not...it doesn't matter.
Release the patches and let the corporate security professionals do the job that they are paid to do.
That is my 2 cents...
Monday, September 25, 2006
Saturday, September 23, 2006
Bin Laden May Be Dead, Reports Claim
NEW YORK (MarketWatch) -- Al Qaeda leader Bin Laden may have contracted an illness and may be dead, according to several news reports Saturday, including Time Magazine.
Time, citing unnamed Saudi sources, said officials have received "multiple credible reports over the last several weeks" that Bin Laden is suffering from a water-borne illness. The source said there is a high probability that Bin Laden has died from the disease, according to Time.
However, the source said there is no "concrete" evidence Bin Laden is dead, according to the report. And Reuters reported that government officials in the United States and France could not confirm details, but French officials did say they had launched an investigation into how a government report making the claim may have been leaked.
French President Jacques Chirac, speaking at a joint press conference with Russian President Vladimir Putin and German Chancellor Angela Merkel in Compiegne, France,, said the Bin Laden's death was "in no way whatsoever confirmed," according to the Associated Press.
A French newspaper reportedly said that report concluded Bin Laden had contracted a serious case of typhoid fever in August and developed partial paralysis as a result. The report said the information came from a "usually reliable source."
Arab diplomats said Bin Laden's health has deteriorated during the last year, forcing him to travel less, CBS News reported. The report also said that Saudi intelligence has very credible information that Bin Laden has been seriously ill and has "a very high certainty" that he is dead.
The report said Saudi officials had their first information on Bin Laden's alleged death on Sept. 4.
A senior White House official, who declined to be identified, doubted the report, CBS said. Other news agencies said the Central Intelligence Agency and White House spokesmen could not confirm reports.Washington-based IntelCenter, which monitors terrorists movements said the last time it could be sure Bin Laden was alive was June 29, when al Qaeda released an audio tape in which Bin Laden eulogized Abu Musab Zarqawi, the Iraqi al Qaeda leader who was killed in a U.S. airstrike that same month.
------------------------
Taken with a gain of salt, of course. The sad truth it wouldn't matter in a operational sense if he dead or alive. But in a pure subjective sense, it might provide some level of justice. Al-Qaeda is less of a structured orginazation and more of than idea. An idea which isn't linked to one man, one group, or even one generation or men.
"Beneath this mask there is more than flesh. Beneath this mask there is an idea...and ideas are bulletproof."
- V (V for Vendetta)
Unofficial Zero-Day Patch for VML Vuln Released by ZERT
ZERT is a group of engineers with extensive experience in reverse engineering software, firmware and hardware coupled with liaisons from industry, community and incident response groups. While ZERT works with several Internet security operations and has liaisons to anti-virus and network operations communities, ZERT is not affiliated with a particular vendor.
ZERT members work together as a team to release a non-vendor patch when a so-called "0day" (zero-day) exploit appears in the open which poses a serious risk to the public, to the infrastructure of the Internet or both. The purpose of ZERT is not to "crack" products, but rather to "uncrack" them by averting security vulnerabilities in them before they can be widely exploited.
It is always a good idea to wait for a vendor-supplied patch and apply it as soon as possible, but there will be times when an ad-hoc group such as ours can release a working patch before a vendor can release their solution.
------------------------
The ZERT's first Zero-day patch has been released.
ZERT2006-01: Buffer overflow in Vector Markup Language (VML) library file used by Microsoft Internet Explorer and Outlook
-------------------------
The ZERT isn't a loose group of no-names.
The member list includes Ilfak Guilfanov, Matthew Murphy, Micheal Lynn, John Cartwright, Halvar Flake, Gadi Evron, Paul Vixie, Nick FitzGerald and others.
Friday, September 22, 2006
All Vista Editions on a Single DVD - The Hacker's Dream
You probably remember the old hack that lets you change a couple of digits in a registry key in order to burn a disc capable of installing Windows XP Pro when all you paid for was the cheaper Home edition. Well it looks like Microsoft is once again looking to save a few bucks at the expense of minimizing piracy, as the company has reportedly confirmed to IDG News Service that every version of Vista -- from Home Basic to Ultimate -- will ship on a single DVD when the OS is finally released. Besides enabling Redmond to cut costs, there are even more self-serving interests at play in this decision: by giving consumers an easy way to upgrade, Microsoft is hoping that more people will drool over the extra features in the pricier packages and decide to throw down the cash for a new registration key. Of course the downside to this strategy is that somehow, somewhere, some clever hacker is going to figure out a way to get Ultimate onto his/her machine without the upgrade fee (after disabling WGA of course), and people the world over with less morals than ourselves or our readers will gleefully follow suit. Anyway, we could never in good conscience recommend that you partake in such illegal activities, but as per usual, you can be sure that we'll be reporting on this hack the minute it hits our tip jar.
MPAA Hires Dogs to Sniff Out Illegal DVDs
LOS ANGELES (Reuters) - This time, Hollywood really has gone to the dogs.
The Motion Picture Association of America on Thursday unveiled its latest tool in the war on movie piracy: a pair of DVD-sniffing Labrador Retrievers named Lucky and Flo.
The MPAA, which represents the major U.S. movie studios in government and legal affairs, claims the illegal copying of movies and television shows on DVDs and other media cost them more than $6.1 billion in lost revenues in 2005.
Of that total, about $2.4 billion was lost to copying movies to videocassettes, DVDs or video CDs. In recent years, the organization has waged a vigorous battle against global piracy.
In July, for instance, the MPAA and foreign government officials wrapped up "Operation Red Card," which resulted in the seizure of some 6.7 million pirated discs in 12 countries across the Asia-Pacific region.
The job for Lucky and Flo will be to sniff out optical discs in luggage or other containers, and stop the discs from getting to manufacturing plants where they can be reproduced.
Apple Updates Airport Drivers
Very interesting. As I stated over a week ago, all the hard headed Mac users that were in deep denial can now rest easy, know that buffer overflows exist in the Airport wireless drivers.
It is amazing how little respect researchers get when they attempt to protect the people in the end put them down. Will we see article in the media that reverse what they said before? Most likely not....
Watch the SANS page for update on this issue..
----------------------------------------------------------------------
TITLE:
Apple Airport Buffer Overflow and Integer Overflow Vulnerabilities
SECUNIA ADVISORY ID:
SA22068
VERIFY ADVISORY:
http://secunia.com/advisories/22068/
CRITICAL:
Highly critical
IMPACT:
DoS, System access
WHERE:
From remote
OPERATING SYSTEM:
Apple Macintosh OS X
http://secunia.com/product/96/
DESCRIPTION:
Some vulnerabilities have been reported in AirPort, which can be exploited by malicious people to cause a DoS (Denial of Service) or to compromise a vulnerable system.
1) Two boundary errors exist in the handling of malformed wireless network frames. These can be exploited to cause a stack-based buffer overflow by sending a malicious frame to the system, and may allow arbitrary code execution with system privileges.
The vulnerability affects the following products equipped with
wireless:
* Power Mac
* PowerBook
* iBook
* iMac
* Mac Pro
* Xserve
* PowerPC-based Mac mini
2) A boundary error exists in the AirPort wireless driver's handling of scan cache updates. This can be exploited to cause a buffer overflow by sending a malicious frame to the system and may lead to a system crash, privilege elevation, or execution of arbitrary code with system privileges.
3) An integer overflow exist in the AirPort wireless drivers API for third-party software, which may lead to a buffer overflow in applications using the API. This can be exploited to cause a buffer overflow by sending a malicious frame to the system and could crash the application or lead to arbitrary code execution with privileges of the user running the application.
Vulnerabilities #2 and #3 affect Intel-based Mac mini, MacBook, and MacBook Pro equipped with wireless and does not affect systems prior to Mac OS X v10.4.
SOLUTION:
Apply Security Update 2006-005 or AirPort Update 2006-001:
http://www.apple.com/support/downloads/
PROVIDED AND/OR DISCOVERED BY:
Reported by the vendor.
ORIGINAL ADVISORY:
http://docs.info.apple.com/article.html?artnum=304420
Thursday, September 21, 2006
Drink Cocaine!
Cocaine - Instant Rush. NO Crash!
Warning! You are about to experience the highest energy content of ANY energy drink on the market today! 350% greater than The Bull!
Cocaine is not just a re-hash of existing drinks: It is a completely unique new formula - it tastes like a fireball, a carbonated atomic fireball!
The question you have to ask yourself is: "Can I handle the rush?"
--------------------------------------
You can currently only get it in Las Vegas and New York, but I am sure this will soon catch on. It contains one of the few sugars, Dextrose, that reduces the "crash" normally associated with power drinks.
Very interesting...
Wednesday, September 20, 2006
Unlocking Windows Laptops with Firewire Crack
Locking your firewire-equipped Windows PC while you pop out for lunch won't keep it secure, thanks to a new hack developed by a New Zealand-based security consultant.
The new attack, which unlocks Windows workstations in 20 seconds by manipulating firewire ports, will be demonstrated at Sydney's Ruxcon security conference on September 30.
"It's generally well known in the forensics community that you can do this; it's just not been done against Windows as far as I know," says the creator of the hack, Adam Boileau, a consultant with Security-Assessment.com. "If you see an exposed firewire port, chances are that dude's got a problem."
By attaching a Linux-based computer running Mr Boileau's software to a locked Windows workstation, the target machine is tricked into allowing the attacking system to have read and write access to its memory, he says. After 20 seconds or so, the software fiddles with Windows' password protection code in the memory of the target machine, rendering it useless.
"You have read and write access to main memory, which means you can overwrite something that's about to be executed with your own code," he says.
The only reliable way to protect a computer against the unlocking technique is to disable its firewire port.
Tuesday, September 19, 2006
Hezbollah Hacked Israeli Radios?
This is downright shocking, if true. "Hezbollah guerrillas were able to hack into Israeli radio communications during last month's battles in south Lebanon, an intelligence breakthrough that helped them thwart Israeli tank assaults," Newsday reports.
Using technology most likely supplied by Iran, special Hezbollah teams monitored the constantly changing radio frequencies of Israeli troops on the ground. That gave guerrillas a picture of Israeli movements, casualty reports and supply routes. It also allowed Hezbollah anti-tank units to more effectively target advancing Israeli armor, according to the officials...The Israeli military refused to comment on whether its radio communications were compromised, citing security concerns. But a former Israeli general, who spoke on the condition of anonymity, said Hezbollah's ability to secretly hack into military transmissions had "disastrous" consequences for the Israeli offensive...
Like most modern militaries, Israeli forces use a practice known as "frequency-hopping" - rapidly switching among dozens of frequencies per second - to prevent radio messages from being jammed or intercepted. It also uses encryption devices to make it difficult for enemy forces to decipher transmissions even if they are intercepted. The Israelis mostly rely on a U.S.-designed communication system called the Single Channel Ground and Airborne Radio System...
With frequency-hopping and encryption, most radio communications become very difficult to hack. But troops in the battlefield sometimes make mistakes in following secure radio procedures and can give an enemy a way to break into the frequency-hopping patterns. That might have happened during some battles between Israel and Hezbollah, according to the Lebanese official. Hezbollah teams likely also had sophisticated reconnaissance devices that could intercept radio signals even while they were frequency-hopping.
During one raid in southern Lebanon, Israeli special forces said they found a Hezbollah office equipped with jamming and eavesdropping devices.
It was my impression that this kind of signal interception was really, really hard to do -- especially for an irregular force like Hezbollah. I know there are some radio and commsec gurus who read the site regularly. Weigh in here, guys.
Or maybe the article itself contains the seed of what actually happened. "Besides radio transmissions, the official said Hezbollah also monitored cell phone calls among Israeli troops," Newsday notes. A raided Hezbollah base had list of "cell phone numbers for Israeli commanders."
Cells are, of course, way easier to intercept. "Israeli forces were under strict orders not to divulge sensitive information over the phone." But maybe they talked anyway. Maybe they thought Hezbollah would never be sophisticated enough to grab their calls.
UPDATE 3:25 PM: Weeks ago, the Times of London and Asia Times had hints of this.
Apparently using techniques learnt from their paymasters in Iran, they were even able to crack the codes and follow the fast-changing frequencies of Israeli radio communications, intercepting reports of the casualties they had inflicted again and again. This enabled them to dominate the media war by announcing Israeli fatalities first.
“They monitored our secure radio communications in the most professional way,” one Israeli officer admitted. “When we lose a man, the fighting unit immediately gives the location and the number back to headquarters. What Hezbollah did was to monitor our radio and immediately send it to their Al-Manar TV, which broadcast it almost live, long before the official Israeli radio.”
HACKTIVISMO RELEASES TORPARK FOR ANONYMOUS, PORTABLE WEB BRO
HACKTIVISMO RELEASES TORPARK FOR ANONYMOUS, PORTABLE WEB BROWSING
Torpark keeps Web surfers' identities private, can run off a USB stick, and scrubs tracks from host computers and browsers.
New York, NY (PRWEB) - September 19, 2006 – Hacktivismo, an international group of computer security experts and human rights workers, just released Torpark, an anonymous, fully portable Web browser based on Mozilla Firefox. Torpark comes pre-configured, requires no installation, can run off a USB memory stick, and leaves no tracks behind in the browser or computer. Torpark is a highly modified variant of Portable Firefox, that uses the TOR (The Onion Router) network to anonymize the connection between the user and the website that is being visited.
“We live in a time where acquisition technologies are cherry picking and collating every aspect of our online lives,” said Hacktivismo founder Oxblood Ruffin. “Torpark continues Hacktivismo’s commitment to expanding privacy rights on the Internet. And the best thing is, it’s free. No one should have to pay for basic human rights, especially the right of privacy.”
Torpark is being released under the GNU General Public License and is dedicated to the Panchen Lama*.
HOW TORPARK WORKS
When a user logs onto the Internet, a unique IP address is assigned to manage the computer’s identity. Each website the user visits can see and log the user's IP address. Hostile governments and data thieves can easily monitor this interaction to correlate activity and pinpoint a user's identity.
Torpark causes the IP address seen by the website to change every few minutes to frustrate eavesdropping and mask the requesting source. For example, a user could be surfing the Internet from a home computer in Ghana, and it might appear to websites that the user was coming from a university computer in Germany or any other country with servers in the TOR network.
It is important to note that the data passing from the user's computer into the TOR network is encrypted. Therefore, the user’s Internet Service Provider (ISP) cannot see the information that is passing through the Torpark browser, such as the websites visited, or posts the user might have made to a forum. The ISP can only see an encrypted connection to the TOR network.
However, users must understand that there are limitations to the anonymity. Torpark anonymizes the user’s connection but not the data. Data traveling between the client and the TOR network is encrypted, but the data between the TOR network and websites is unencrypted. Therefore, the user should not use his/her username or password on websites that do not offer a secure login and session (noted by a golden padlock at the bottom of the Torpark browser screen).
DOWNLOAD TORPARK
http://torpark.nfshost.com/download.html
Press Contact
press@hacktivismo.com
ABOUT HACKTIVISMO
www.hacktivismo.com
Hacktivismo is a group of international hackers, human rights workers, artists and others who seek to further the goals of human rights through technology. They operate under the aegis of the CULT OF THE DEAD COW (cDc). Hacktivismo is committed to developing technologies in support of the highest standards of human rights.
ABOUT THE CULT OF THE DEAD COW
www.cultdeadcow.com
CULT OF THE DEAD COW (cDc) is the most influential hacking group in the world. The cDc alumni list reads like a Who's Who of hacking and includes a former U.S. presidential advisor on Internet security, among others. The group is further distinguished by publishing the longest running e-zine on the Internet [est. 1984], stretching the limits of the First Amendment, and fighting anyone or any government that aspires to limit free speech.
* ABOUT THE PANCHEN LAMA
www.savetibet.org/news/positionpapers/panchenlama.php
The Panchen Lama is often referred to as the world’s youngest political prisoner. In May 1995, agents of the Chinese government kidnapped the six-year-old Panchen Lama and his parents. They have not been seen or heard from since, despite repeated calls from the United Nations and international human rights organizations. Chinese officials claim that the Panchen Lama is being held in “protective custody”. Six months after the abduction, China installed its handpicked version of the Panchen Lama. The boy is forced to act as a mouthpiece for Chinese policy in Tibet, and is referred to as “the fake” by Tibetans.
###
from http://www.prweb.com/releases/2006/9/prweb438978.htm | pdf version
Sunday, September 17, 2006
SF: A Question of Ethics
My Consciousness - Part 1
Who am I? Why am I here? What makes me different than those around me? Perhaps these questions can never be answered, but I believe I can find answers that work for me....answers that allow me to move on...answers that allow me to live...answers that allow me to be happy. Don't we all just want to be happy in the end? I am sure my answers will not be like the answers of others, but isn't that the point? What I see as answers may only appear as more questions to the person that just handed me my coffee. I believe the answers are non-static and they cannot be set in stone, they are fluid, they are dynamic, they are the process of searching…
The process by which a thought becomes an idea is simple, yet cannot be measured, explained or classified by the scientific world. The brain might be the most complex thing that we have ever attempted to study. It is specialized yet decentralized. It is divided into two distinct halves, yet they work together on even the simplest task.
Friday, September 15, 2006
New IE Zero-Day and Fresh Out of the Oven Firefox Updates
Security researchers in China have published detailed exploit code for a new zero-day vulnerability in Microsoft's dominant Internet Explorer browser.
The exploit, which was posted to XSec.org and Milw0rm.com Web sites, could be easily modified to launch code execution attacks without any user action on fully patched Windows machines.
A spokesman for the MSRC (Microsoft Security Response Center) said the company is investigating the latest warning, which adds to a list of known high-risk vulnerabilities that remain unpatched.
Via SANS ISC -
My Firefox just jumped up at me and said "You have some updates".
Version 1.5.0.7 to be exact. So what's new? Well, Mozilla tells us over here.
MFSA 2006-64 (which, by the way, stands for Mozilla Foundation Security Advisory) -- "Crashes with evidence of memory corruption" Mozilla says, "...we presume that at least some of these [bugs] could be exploited to run arbitrary code with enough effort." So, get your patches!
MFSA 2006-62 -- Popup-blocker cross-site scripting (XSS)
More XSS stuff, except this time against the Popup-blocker feature. Mozilla doesn't really view this as a big threat: "The malicious page would first have to get itself framed by the target page, attempt to open a popup, and then convince the user that the popup contents were so important or interesting that it must be opened manually."
MFSA 2006-61 -- Frame spoofing using document.open()
This vulnerability is kind of a reshash of this one. "The victim site must first be opened in a new window (or tab) by the malicious site for this flaw to work." Basically, be wary of any sites or windows, not opened by you.
MFSA 2006-60 -- RSA Signature Forgery
Looks like Philip Mackenzie and Marius Schilder over at Google found this one.
"Because the set of root Certificate Authorities that ship with Mozilla clients contain some with an exponent of 3 it was possible to make up certificates, such as SSL/TLS and email certificates, that were not detected as invalid. This raised the possibility of the sort of Man-in-the-Middle attacks SSL/TLS was invented to prevent." Good, I read about this one not too long ago on a couple mailing lists that I lurk on.
MFSA 2006-59 -- Concurrency-related vulnerability
Mozilla has this to say: "We have seen no demonstration that these crashes could be reliably exploited, but they do show evidence of memory corruption so we presume they could be."
MFSA 2006-58 -- Auto-Update compromise through DNS and SSL spoofing
DNS and SSL spoofing vulnerability. Mozilla does offer some good advice on this one:
"Do not accept unverifiable (often self-signed) certificates as valid. If you must, accept them for the session only, never permanently." Rule of thumb.
MFSA 2006-57 -- JavaScript Regular Expression Heap Corruption
"...a regular expression that ends with a backslash inside an unterminated character set (e.g. "[\\") will cause the regular epression engine to read beyond the end of the buffer, possibly leading to a crash."
... and since Thunderbird uses the same browser engine as Firefox, you need to update it too!
Thursday, September 14, 2006
DHS Releases Cyber Storm Report
The U.S. Department of Homeland Security (DHS) released its public findings from Operation Cyber Storm, a large-scale tabletop simulation of a coordinated cyber attack on the government and critical infrastructure that was held in February, 2006.
The exercise involved US-CERT, the Homeland Security Operation center as well as the National Cyber Response Coordination Group (NCRCG) and the Intragency Incident Mnagement Group (IIMG), various ISACs from the transportation, energy, IT and telecommunications sectors, and 100 private sector companies including Microsoft and VeriSign.
The report was released by DHS's National Cyber Security Division (NCSD) Wednesday and while no performance "grade" was assigned, read between the lines of the public report and the term "Needs Improvement" comes to mind.
The exercise simulated a large-scale cyber campaign that disrupts multiple critical infrastructure, as well as simulated "physical demonstrations and distrubances" to test the ability of government to respond to multiple incidents simultaneously, even when its not clear that the events are related (read: 9/11).
So how'd our government do? Not so well.
In a way, I am glad the government didn't "pass with flying colors". This leads me to believe that the test was created to truly challenge the departments and response teams. Like any DR test, the first one is almost always a total write-off. Lets just make sure we do what we need to do...and we do better next time.
Wednesday, September 13, 2006
THC and The Nokia Rom Images
THC and The Nokia Rom Images
2006-09-06
In mid july Nokia charged THC with copyright infringement and threatenedwith a lawsuit. THC took down thc.org to prevent further cost and alegal disaster.
A month earlier THC discovered significant security flaws in Nokia'sOperating System. To proof it THC published ROM images of 3 phones.THC did not publish the source code or tools but one thing becameapparent: To extract the ROM images core security features had to bebreached. THC's ability to load kernel modules and gain access to thecore of the OS (including the GSM stack) was something Nokia did notlike.
At the time of the release THC was not aware of any copyright protectedmaterial inside the roms. The question has to be asked if Nokia chosed the right method by threatening THC with a lawsuit or if an email couldhave achieved the same. Was their concern really copyright infringement? The software in the rom-images could not be used, not be ported and not berun on any other mobile phone. In addition all software is already availableon every phone. Phones that are given away by the mobile operators for1 Euro or sometimes even for free. So if everyone has access to the software anyway what is the point in threatening THC? What was their real intend? Wemight never find out. But what we know is that they managed to silence THC for a month.
If this is professional practice? We do not know. It is certainly the practice that Nokia chose. We also know that no attempt was made by Nokiato inquire about the security vulnerability. We also know that Nokia didnot provide any updates for their customers.
Making sure that the hardware we purchase is secure is not a crime.In fact taking a look at what we buy should be our duty. We should nottrust big corporates who claim in TV advertisements how secure andsafe our data is. We have to test it and proof them wrong whenever wecan.
In fact researchers should demand that manufactures like Nokia mustprovide full documentation of their hardware. The buyer becomes the ownerof the mobile phone and thus has the right to know how to program thehardware. Nokia does not provide any of such information. Free softwareor a different operating system can not be used because of limited accessto documentation. This is a classic example of a hardware giant allowingonly his own software to be used. This is what some people would considera Monopoly and an abuse of power.
THC is deeply concerned that Nokia did not choose the diplomatic route.
THC also released a Nokia Unlock Tool that removes the phone lock protection by exploiting a design flaw in the moblie phone. The tool does not remove the sim-lock however.
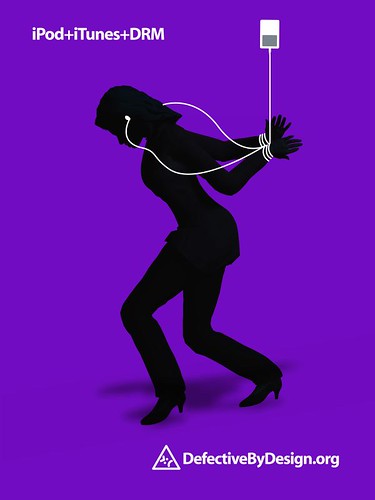
October 3rd Declared "Day Against DRM"
Tuesday, September 12, 2006
Vulnerabilities Released Today
- Microsoft Publisher Code Execution Vulnerability (Issued 1 Hour ago)
- Microsoft Windows Pragmatic General Multicast Code Execution - requires MSMQ service to be installed. (Issued 2 Hours ago)
- Adobe Flash Player Multiple Unspecified Vulnerabilities (Issued 30 mins ago)
SF: Analyzing malicious SSH login attempts
This SSH Scanner sounds like a pretty smart IRC bot spreading method...
Friday, September 8, 2006
PCI DSS Standard v1.1 Released
Here is the full PCI DSS v1.1 PDF
I haven't had a chance to fully read over it...
Microsoft Patch Tuesday - Advance Notice
Two Microsoft Security Bulletins affecting Microsoft Windows.
The highest Maximum Severity rating for these is Important.
These updates will be detectable using the Microsoft Baseline Security Analyzer (MBSA).
Some of these updates will require a restart..
One Microsoft Security Bulletin affecting Microsoft Office.
The highest Maximum Severity rating for these is Critical.
These updates will be detectable using the Microsoft Baseline Security Analyzer (MBSA).
These updates may require a restart.
Thursday, September 7, 2006
Tools of the Trade
1) Yesterday (9/6/2006) Michal Zalewski released p0f v.2.0.8
P0f is a very slick passive operating system fingerprinting tool. It provides features that you won't find in the great active scanner - masquerade detection, thru-firewall fingerprinting, profiling network topology distance and netlink information, etc.
2) Earlier this week, a security advisory was released for OpenSSL.
It appears that with the right conditions it is possible for an attacker to forge a PKCS #1 v1.5 signature that was signed using a RSA key with exponent 3.
Upgrade to 0.9.7k or 0.9.8c
3) On Aug 30th, Tenable Network Security released Nessus 3.0.3 Beta 14 for Windows.
If you are using Tenable Security Center to manage your Nessus installs, make sure you read the release notes for Beta 14.
4) On Aug 28th, my friend HD Moore released Metasploit Framework (MSF) 3.0 Beta 2.
Beta 2 is fully compatible with Linux, BSD, Mac OS X, and Windows using their custom Cygwin installer. MSF 2.6 and MSF 3.0 can be installed on the same computer; just don't run them at the same time. Please be aware that the web console is awaiting a serious re-write and therefore does not work very well in MSF 3.0. ;)
5) On Aug 28th, Snort was updated to 2.6.0.1
Martin Roesch noted on Packetstorm that new changes were added to allow configurable dropping of decoder alerts in inline mode. Updates were also added to the Oracle database plugin to handle large data blobs and graceful disconnection.
6) On Aug 23rd, Wireshark 0.99.3 was released.
It fixed several security issues, added support for several new protocols. See the release notes for the full details.
7) On Aug 1st, GnuPG 1.4.5 was released.
It included a moderately critical security fix and several tweaks.
Malware Using Built-In EFS as Protection
Recently a trojan was seen to take advantage of EFS to protect itself and execute with administrative privileges. This malware is composed of obfuscated DLL and PE files that are thoughtfully crafted. It has two main components, a dialer component that is detected as Qdial-45 the other is a downloader/dropper component detected as Spy-Agent.bf that drops this dialer along with an EFS encrypted downloader file. McAfee has been detecting variants of this trojan since August 02, 2006, however we have observed an upsurge in infection rates in last few weeks.
Tuesday, September 5, 2006
Using Old Tricks to Steal New Cars
A group of hijackers has used an old but still effective way to distract their victims’ attention at one of beaches near Moscow. The criminals brought with them three girls who bathed naked while they successfully stole four cars.The Moskovsky Komsomolets daily reports that the incident took place in the Moscow suburban town of Balashikha in late July.
People were relaxing at a river beach when a Toyota SUV stopped by and three beautiful girls got out of it. Eyewitnesses report that the girls fully undressed went knee-deep in the water and played there for a while.Naturally, all attention was drawn to the girls who were later described by the victims as the complete resemblance of adult magazine models. Suddenly, the naked bathers got back into the SUV and quickly drove away.
Only then did the people on the beach realize that four cars had been stolen. Other cars were broken into and various valuables were stolen as well
Johnny Cache, Blackhat & Wireless
I would tell Johnny to not let the Mac Blind get to him. Johnny doesn't need to take bets or prove that Apple has vulnerabilities to every other Mac user. Apple OSX has had vulnerabilities...and it will have more in the future. Stop crying and think about what you are going to do to protect yourself.
If / When Apple releases patches for its wireless products, we will all have the true answer to the question that is bugging everyone. That is if Apple tells us the real reason they are issuing a patch....at this point, I see no good reason why Apple would want to tell their general users the truth. Their general user already believes they don't have anything to worry about anyways.
I am sure the patch will be released on the first Tuesday of the month; under cover of a zero-day Windows patch...lol
I do agree that some of the media have blown the issue out of the box and applied strange negative spin to the real issue.
Real Issue = Device Drivers, as a whole, should be lookedb at as possible attack vectors and manufacturers need to start giving the same security attention to device driver code that they give to normal application code. Period.
Malware Found Using Another Office Zero-day
These attacks are normally targeted and present a lower risk to the general public. Secunia has tagged it as SA21735.
Check out this Symantec write-up - "New Tricks with Old Software - New Zero-Day in MS Office 2000".
SecuriTeam has also released a FAQ on this one. Very good stuff.
No patch date has been suggested by Microsoft at this point.
Sunday, September 3, 2006
New Al-Qeada Video
I was able to find, acquire and view this video just now. It is quite rare for me to be able to find it so fast.
It is a very long video, basically 45 mins, which amounts to a 500 MB MPEG file. But they always supply multiple links to lower quality realmedia versions as well.
The production quality is better than I have seen from other groups. It contains both English and Arabic subtitles, where removed the need for translation. Graphics are also very high quality.
On August 31st, As-Sahab released an advertisement for the upcoming video.
"Adam" is from Cali and is seen in the video as "Azzam the American". He spoke English mostly and talked about many political issues beyond what is described in the SITE article.
Read more about the content of the video over at the CounterTerrorism Blog.
Saturday, September 2, 2006
Walt Disney World Fingerprints Visitors to Fight Ticket Fraud
Disney is now fingerprinting visitors to Walt Disney World as part of its ticket-fraud prevention scheme. They're not being very transparent about it, either: there are no signs posted about the data collection or retention, and Disney's official line is that they're not collecting fingerprints, just mathematical representations of same.
Ummm, not taking fingerprints, just storing the mathematical representations collected by analyzing several key and unquie points in the fingerprint. Isn't that the how all fingerprints are taken? I believe so...which makes their statement crazy, IMHO.
Yet another reason never to go to Disney World.
Myspace and WMF Exploits
A profile that was linking to a WMF trojan.

Strange Friend Request

Trojan Hosted in the US and linked by Myspace profile
The profile ID and the IP address have been reported to the parties involved at the time of my writing.
This is just one example and this isn't a new. Myspace and the other social sites have become easy picking grounds for wrong doers. Corporations, schools and people must not be tricked by the false sense of community created by these sites.
I would bet 100 dollars that Mr Greenlee Lite is in my "Extended Network" on Myspace. Why and how?
Because Tom is automatically added as your friend upon sign-up, which in turns means everyone with Tom as a friend is automatically in your Extended Network. Even if you delete Tom, if one of your friends or one of their friends has Tom as a friend...it is still useless.
So why does the "Extended Network" even exist? To create a false sense of safety and community. Period.
Moral of the Story - Be careful out there, dangers are around every corner...
Friday, September 1, 2006
Black Rock City Rises from the Sands of the Desert

You might remember last year's Dance Dance Immolation

Burning Man 2006: Aug 28th - Sept 4th
http://www.burningman.com/
http://en.wikipedia.org/wiki/Burning_Man